Is my school at risk of a cyber-attack?
Cyber Security is on the increase, and whilst some schools are now taking it seriously and making changes, many are not. Wherever you are on your Cyber Protection journey, this blog should help you create a definitive plan should you be attacked by a hacker or other malware programmes.
How likely are we to receive a cyber-attack?

In 2019, two thirds of all organisations reported some type of incident relating to cyber-crime.
You could make a sure bet this figure rose significantly last year, thanks to criminals taking advantage of the pandemic.
How much is the average loss after a cyber-attack?
The average cost of a data breach to a business is estimated to be around £337,000. Even though a school is not a corporate business, it is still vulnerable to financial loss, and with today’s budgets, any loss can be catastrophic. A school can be crippled by an attack, as teaching hours are taken away, and money lost to ransom.
What are the most common types of cyber-attack?
Ransomware, where your data is locked away until you pay a ransom fee.
Phishing, where criminals pretend to be someone else, to get you to click on a bad link, they can then gain access to critical systems within the school.
School funds are then lost due to:
- Any ransom demanded by criminals who lock your data and remove your access to it.
- The cost of recovering your data, and undoing the extensive damage done.
- Putting in place additional ongoing security measures after the breach.
- Paying for goods and services that are being provided by a genuine service provider, but where the invoice had been intercepted and altered to pay a third party.
On top of the financial impact, there is also the reputational one.
How do we safeguard our reputation after a cyber-attack?

Could you imagine picking up the phone to every parent and stakeholder, to tell them your data about them had been accessed and stolen? And was probably for sale on the dark web?
What would happen if the local media or news blogs got hold of this and ran a story about it?
You have to ask yourself very carefully: Could your school afford to be hit by a ransomware or phishing attack?
Truth is that many schools really couldn’t.
So why do so few education establishments have a plan in place to a) prevent and b) respond to cyber-crime?
Does your school have a cyber-crime action plan in place?
If not, it is time to do something about it, as there has been an explosion in the number of ransomware and phishing attacks over the past couple of years.
If you don’t have an effective plan in place to help keep your school business protected – and to minimise damage should the worst happen – you’re leaving yourself vulnerable.
Cyber-criminals are targeting everywhere, all the time, using clever automated tools that sniff out vulnerabilities. So it’s only a matter of time till your school’s defences are tested.
What steps should I take to prevent being hacked?
Here’s our recommended 5 step plan to prepare for an attack, and protect your school.
1) Training, training, training
Believe it or not, your devices and software are not the weakest link in your defence. Your people are.

Your team’s awareness of the risks, and their mindset towards spotting risks and acting on them, can make a dramatic difference towards your chances of being affected.
Although they would never knowingly do a thing to damage the school infrastructure or administration, all it takes is one click for them to bring you down.
One click. On one bad link. In one email.
Phishing scams are getting more sophisticated every day, and they are really easy to fall for. You don’t have to be an 80 year old email newbie to fall for a phishing scam these days. With some of the smartest social engineering, even the wariest person can be caught out. 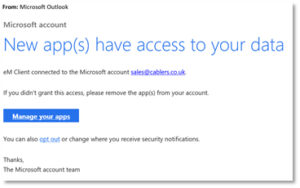
Fortunately, with the right training, your team can be taught the tell-tale signs of a scam email, looking at:
- The email address it was sent from
- Who it is addressed to
- Language used
- Font and design of the email
- How to check if a link is safe before clicking on it
There are other things that cyber security training can teach your people.
Things like closing RDP links; a techy term for a connection from your computer to another.
And looking out for signs you are under attack from ransomware.
Plus other areas of online safety that you may not usually discuss. Such as what information criminals can glean from social media.
There is a lot that can go wrong online. And the more people you have working for you, the greater your risk of one of those things happening to your business.
All staff should have regular cyber-security awareness training – including you.
Things change so frequently that it really is in your best interest to keep everyone’s knowledge topped up.
Check out the National Cyber Security website for more information on keeping your school safe: Click here for the article
They also provide an Exercise in a box, which they promote as “an online tool from the NCSC which helps organisations test and practise their response to a cyber attack. It is completely free and you don’t have to be an expert to use it.” Click here for the link
2) Use the tools available to you
There are a lot of tools out there to help keep your business safe and protected from cyber-criminals. Make use of them.
Some of the most commonly used tools are:
Password managers: These generate long random character passwords for new applications and remember them so you don’t have to.
- Multi-factor authentication: This is where you enter a code from another device, to prove it’s really you logging in.
- VPNs: A Virtual Private Network gives you a secure connection to your business when working remotely.
- Encryption: This makes the content of your devices look like thousands of random characters to anyone without the encryption key. So, it’s only a minor inconvenience if you lose a device, not a major catastrophe.
- Anti-Ransomware software: standard antivirus software will not protect your data from a ransomware attack, it is critical to ensure that your school has anti-ransomware software installed.
These are just the basics. There are always extra layers of cyber security available.
Yes, this is complicated, and there are too many options to choose from. The trick is putting together the right blend of security tools for your specific circumstances. So you’re protected, but your security is not stopping your team from getting on with their work every day.
Your IT support provider will be able to make some recommendations. If you’re in the fortune position of having an IT partner, they will work closely with you to understand how your business works inside and out, before making recommendations.
3) Back-up all data, all the time

We cannot stress this enough: if you don’t already have an automated back-up of your data every day, and at the very least the admin data is kept somewhere other than your schools’ premises, arrange this today.
It. Is. Critical.
Keeping a copy of all your data in this way is your fall-back option. If anything ever goes wrong and your data is lost, corrupted, or held to ransom, you retain a copy of everything you need to keep your school functioning.
If you already have off-site back-up in place, well done. Now check that it is working as it should be. This is a process known as verification, and it needs to be done every day.
You’d be surprised to learn how many people leave their back-up unchecked until they need it… only to find the back-up stopped working a few days earlier; or the data was corrupted.
4) PPP
Create a policy, protocol, and procedure in the event of a data breach. Sounds obvious, but this needs to be done before your school has a cyber security problem.
Your policy will set out how your school will deal with any form of data breach or cyber-attack.

Make your policy as detailed as possible, as it is a guide for your establishment to reach the most desired outcome (in this case, minimal impact from an attack).
Include the things your people must do as a minimum to help keep the business safe, such as using a password manager and multi-factor authentication.
Every member of teaching and administrative staff should have a copy of this policy, ideally in your employee handbook. Maybe you could even get them to sign that they have read and are committed to it. That way, no-one can plead ignorance if they have directly put the school at risk.
Your protocol is a written plan that contains the procedures your people must follow in the event of a cyber-attack.
And the procedures you should include are:
- Who to alert in the case of a suspected breach.
- What are the steps that person should take to try to block the attack?
- How everyone else within the business should react.
It is a good idea to include a procedure for lost or stolen devices too, so they can be wiped remotely for ultimate peace of mind.
Make everything in your PPP as accurate and detailed as it can be, so that people are left in no doubt exactly what they should do.
5) Bring in the experts
If you are not an IT expert, a lot of this can seem very time consuming and complicated.
We completely get that.
However, you should understand that it is very much a worthwhile investment of your time and energy.
If you feel it is not something that you can do justice to, it is a smart idea to bring in the experts.
A great IT support provider or partner – should be more than willing to help you.
A good IT company will assess your IT provision and provide a check list on changes that need to happen to enable your system to be as resilient as possible.
You should also have someone to monitor and maintain your devices and network, to identify and solve the majority of issues before you even notice them.
And someone who can make sure you are using all the right tools and software to optimise both security and staff productivity.
Often, it is unrealistic to have a full-time employee on your team to do this work for you. Fortunately, outsourcing is a superior alternative in most cases.
Not only do you get support when you need it, and benefit from all the above, but you also get access to a whole array of expertise.
If you don’t already have a plan in place to keep your business protected from cyber-attack, I hope you can see how vital it really is.
If you do have a plan, perhaps it is time to revisit it and make sure it is still effective in this ever-evolving world of cyber-security and cyber-crime.
And if you find you could do with some honest, expert help and advice, we’d love to be of service. Let’s talk. Click here to book your 15 minute call with Murray.



